By Jim Ligotti, Maritime Solutions
Ingersoll-Rand Security and Safety
Clearly, the maritime industry is one of the most powerful drivers of international commerce and economic vitality in the world. The statistics are astounding:
• The worldwide fleet of marine containers - a transportation cargo unit that can hold up to 500 computer monitors - is nearly 11 million.
• The European Union, which is the main trading partner for two thirds of the world, in 2001 exported EUR 981 billion and imported EUR 1,027 billion.
• The global ocean-liner shipping industry owns approximately $155 billion in vessels, containers, marine terminals and other direct operating assets now in service around the world.
• Almost 16 million Americans work in port-related jobs, producing $210 billion in federal, state and local taxes annually.
Yet only recently, with the introduction of a new body of international regulations called the International Code for the Security of Ships and of Port Facilities (ISPS) have port and vessel companies and agencies been compelled to implement security and safety measures on a comprehensive, international scale. Now, these companies and agencies are struggling to implement security and safety measures that are both reliable and cost effective. Many are finding that conventional approaches to security and safety possess too many limitations to fulfill both of these goals.
Fortunately, there is a better approach for securing ports and vessels - one that can enhance the effectiveness of technologies such as electronic-access control, time-and-attendance, and closed-circuit television (CCTV) monitoring while also improving business efficiencies. It can help operators of ports and vessels save money while protecting their most vital assets.
Through its Maritime Solutions group, Ingersoll-Rand now is bringing this strategy and expertise to ports and vessels around the globe.
ISPS
Two months after September 11, 2001, the IMO agreed to develop "new measures" for enhancing the security and safety of ships and ports. By December 2002, the IMO had defined and ratified its comprehensive approach as the International Code for the Security of Ships and of Port Facilities (ISPS).
The ISPS code's primary objectives are to establish a framework for the IMO's "contracting" governments to cooperate in taking preventive measures against security and safety threats that could affect the maritime industry. The ISPS code also outlines a methodology for ports and vessel operators to assess their particular levels of security risk and describes mandates they must fulfill to comply with the code.
As required by the ISPS, contracting IMO governments have begun to pass legislation that mirrors the requirements and deadlines for compliance outlined by the new code. The 2002 U.S. Maritime Transportation Security Act, for instance, required the 300 coastal and interwaterway ports of the U.S., and the thousands of vessels that dock at them each year, to define their security plans by December 31, 2003. It also requires operators to implement security measures outlined in the Act by the same deadline provided under the ISPS: July 1, 2004.
In the U.S., the Coast Guard, working with government agencies such as the Department of Homeland Security, is responsible for monitoring compliance at ports and vessels.
What the ISPS Means for Ports
and Vessels
ISPS requires companies and agencies involved in maritime trade to implement an unprecedented range of security and safety measures. For many port and vessel operators, the process of installing security systems that comply with the new requirements will continue to be a daunting task for the foreseeable future. Some of the concerns that industry now faces include:
• The high costs of compliance. Although contracting governments are obligated to help fund the costs of added security in their country, the financial burden of installing new equipment, training people and managing new security systems ultimately resides with port and vessel operators. For many operators, the question of how they will fund the high costs of compliance — an ongoing operational cost — the single biggest concern they have with the new legal requirements.
• Best efforts may not be not good enough. Never before have port and vessel operators been required to comprehensively assess their security needs and implement a plan for reliably reducing security and safety risks.
For these operators, the process of outlining and implementing an effective plan that both meets regulatory requirements and stays within the limits of their operational cost structure may be a challenge they are unable to fulfill, despite their best efforts.
• Minimal compliance (or none at all). It is likely that many ports and vessels will try their luck, waiting to see what actions enforcement agencies take with others who are noncompliant before deciding to make a full commitment to security and safety. While some may slip through the cracks for a time, most who fail to comply face stiff fines and lost business opportunities from boycotts by other ships and ports.
• Increasing legislation. The ISPS is divided into two sections: Section A, which describes currently mandated security measures, and Section B, which outlines additional steps ports and vessels may decide to take to enhance security and safety based on their individual level of risk. Some companies already have begun to implement elements of Section B both as a "best practice" and in anticipation that the measures it describes will eventually reflect required practice.
About Conventional Security and Safety Systems
The face of security and safety has changed little during the last century. Although new state-of-the-art technologies such as CCTV monitoring and digital-video recording (DVR) are rapidly replacing or supplementing mechanical lock-based solutions, almost all conventional security and safety systems available continue to be built around the same four fundamental characteristics that such systems have shared for decades. Typically, these characteristics result in systems that are unreliable at promoting security and safety and are difficult and costly for the average business and government agency to implement and manage. These four characteristics are:
• Security specific. Most conventional security and safety systems work in a vacuum, divorced from other business processes. These conventional systems in no way help to enhance business productivity or otherwise assist managers in running a stronger, more efficient business.
• Paper based. Conventional security systems typically rely on paper forms of identification (I.D.), such as drivers' licenses and social security cards, to verify the identity of individuals looking to access secure areas of a facility. Paper forms of I.D. — which colleagues can share and criminals can steal or forge - are inherently unreliable when used to verify identity. The process of screening paper-based I.D. typically requires recording data, such as a driver's license or Social Security number, by writing it down or making photo copies - a time consuming process that risks infringing on privacy rights.
• People driven. In order to screen paper forms of I.D. and track the movement of individuals throughout a facility, an organization needs to employ security personnel. Security personnel are often difficult to train, costly to hire, and undependable.
• Point oriented. Conventional security systems are designed to secure specific points, or areas of concern, at a facility. Specific points include cargo, entrances to a vessel, and equipment. Because conventional approaches focus on specific points, one facility may have several disparate security systems serviced by different vendors. For instance, a CCTV system installed by one vendor for monitoring cargo may work independently of an access-control system installed by another vendor for granting access to truckers who transport cargo. A facility that relies on point-based solutions is invariably inefficient, poorly accommodates change and growth in security needs, and can quickly become unmanageable.
For certain applications, conventional security systems that use decentralized paper- and people-based systems may be a reasonably effective, if not optimal, approach for promoting reliable security and business efficiency. The manager of a small corporate office with a couple dozen employees and a handful of daily visitors, for instance, may determine that hiring a security guard or two to screen building badges suffices for the company's security needs.
But in the complex world of maritime trade — where hundreds or even thousands of crew members, drivers, maintenance workers, administrators and longshoremen, employed by unaffiliated companies and agencies, work together to move goods in and out of a port - a system of security that relies on paper and people to track, manage and monitor vulnerable assets is both inefficient and undependable.
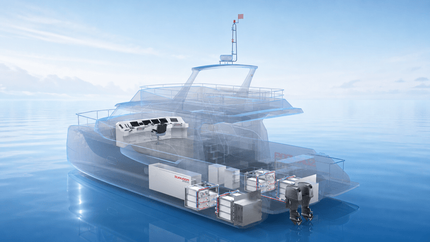
The IS Solution
Ingersoll-Rand has developed the IS, or Integrated Security solution. At the heart of IS is the process of integrating the security and safety requirements for every element of, and activity that takes place, at a facility. These elements and activities may be categorized as people, openings, and assets. For instance, a ship's "openings" include the engine control room, electrical control/equipment room, cargo storage area, bridge, and steering gear room. A port's "people" include longshoremen, crew, administrators, maintenance workers, and truck drivers. Assets for both a port and vessel may include the vessels themselves, equipment, vehicles, containers and cargo. Integrated Security connects people, openings and assets together through a connected information-technology infrastructure based on an expandable, open architecture. Data is generated through the power of electronics — access cards with electronic codes or biometric identifiers replace paper forms of I.D. and significantly reduce the number of security personnel required for security screening. Because the architecture is open, the system easily accommodates the addition of new security applications (i.e., a remote-monitoring system) as modules to a shared database. The result is a highly reliable system that coordinates remote-monitoring, access-control, time-and-attendance, CCTV surveillance and other technologies and processes designed to secure a facility's assets. (See Table 1 below).
Examples of how IS can help a typical port and vessel enhance security and safety while also promoting efficiencies include:
• Track crew at ports of call. Under the ISPS, vessels must maintain and manage records showing the last five ports each member of its crew last visited. While a conventional security system using paper-based tracking systems would be hard pressed to fulfill this challenge, Integrated Security combines time-and-attendance with access-control technologies to generate easily the required information when required.
• Improve productivity of truckers. Truck drivers typically have no way of systematically alerting a vessel's crew of their arrival time at a port. When they arrive, drivers must wait for crew to prepare cargo for transport - a poor use of time that likely adds up to millions of dollars in lost productivity for a typical shipping company. Using IS, registered drivers can electronically signal their scheduled time of arrival in advance so that when they arrive, cargo is ready for departure.
• Automated response to different security levels. If an emergency or threat to security arises, IS can quickly adopt different levels of access control, such as might be defined according to different MARSEC levels, for authorized and unauthorized individuals. For instance, in an emergency that requires people to exit a vessel quickly, through IS, all major exits can open rapidly and automatically. For another threat, a IS system may close certain exits or allow only individuals with a specific authorization to pass through them.
• Minimize costs for damage claims. Although many port managers contend that their facilities are responsible for no more than one third of the total cost they pay annually to settle damage claims for damaged containers, they traditionally have not had a mechanism for proving their innocence. By facilitating the generation of easy-to-navigate reports and video clips that demonstrate at what time and location a particular container was harmed, Integrated Security helps to minimize costs associated from unfair claims.
• Identification Cards. The IMO has called upon contracting governments to issue "seafarer" identification cards that can be used to verify an individual's identity to all personnel involved in the maritime transportation industry. In similar fashion, the U.S. is finalizing plans for a prototype phase of the Transportation Worker Identification Credential (TWIC), an electronic "smart card" that contains coded information, such as biometric identifiers and bar codes, for the 15 million transportation workers in the U.S. who need access to secure areas of airports, seaports and land border crossings. As an approach that relies on electronics and biometrics to verify identify, IS can readily accommodate the seafarers, TWIC and other identification card requirements.
About the Author
Jim Ligotti is vice president for Maritime Solutions within Ingersoll-Rand Security and Safety Solutions, which specializes in implementing integrated security and safety systems across one or more facilities.
Sponsored Content
Canada and Norway Launch a Cross-Atlantic Alliance for Marine and Clean Technologies

Sunwoda Unveils Full Marine Battery Portfolio: From Proven Cells to Scalable Electrification Solutions

May 2026


Trite but true, the path to decarbonization has no ‘silver bullet’ solution.
Read the Magazine
Finding Strategic Support in a Complex Maritime Environment
Vessels
Subscribe for
Maritime Reporter E-News
Maritime Reporter E-News is the maritime industry's largest circulation and most authoritative ENews Service, delivered to your Email five times per week